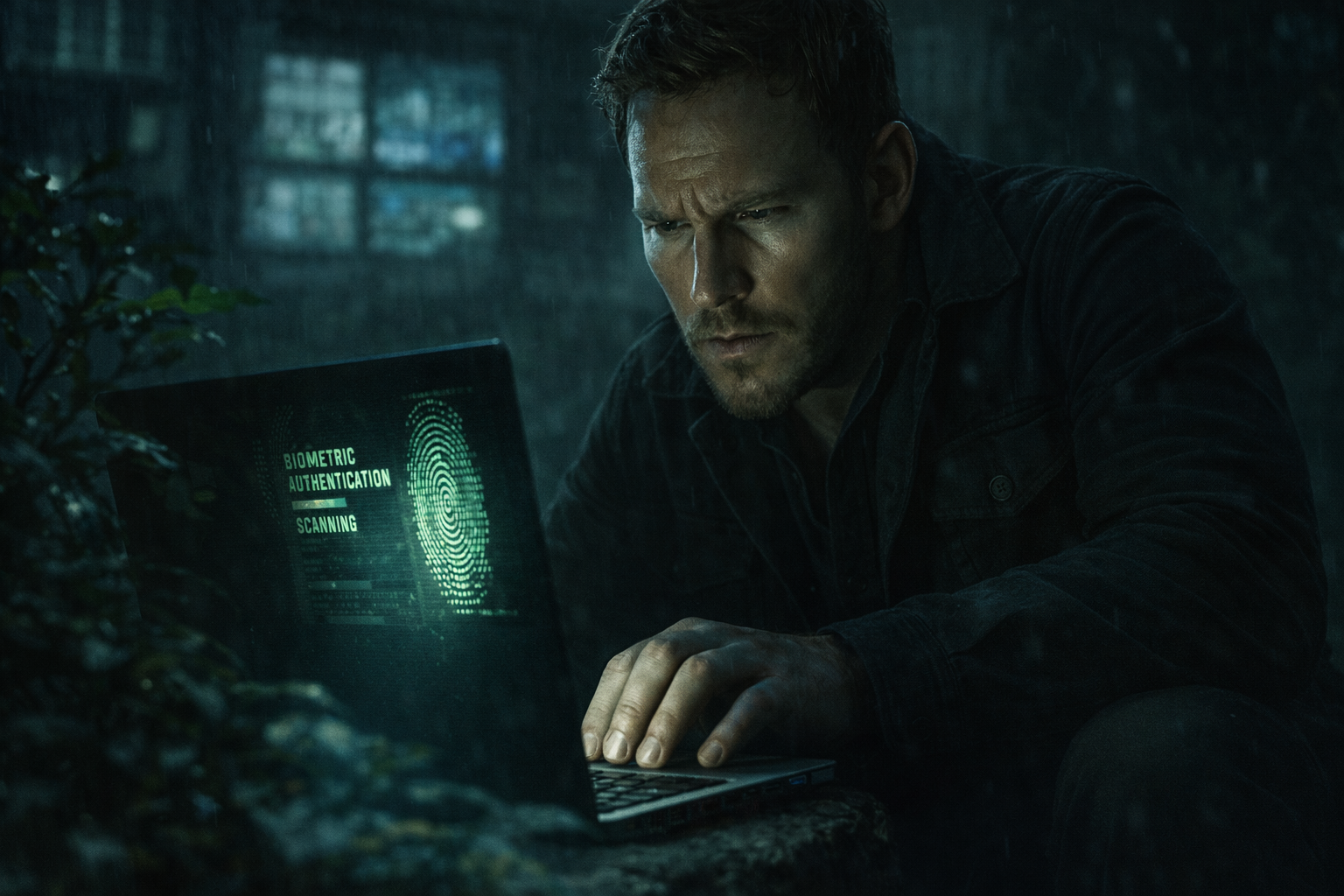
Not Hollywood Hacking — Real Tradecraft
One thing readers keep saying about THE FALLEN is this:
“This feels real.”
That’s because it is.
Micah’s actions in the book use real-world intelligence techniques, including:
SIM Cloning – Creating a duplicate of a phone’s SIM card to quietly monitor calls, texts, and data without the user knowing.
Keylogging – Software that logs keystrokes to capture passwords, messages, and searches as they are typed.
Biometric Phone Access – Unlocking a device using fingerprints or facial recognition just like the owner does.
Geo-Placement Verification – Capturing accurate location data to verify where a device truly is—and if it has been moved or tampered with.
Covert Device Compromise – Gaining hidden access to a phone or computer to monitor activity without leaving visible traces.
Real fact: These aren’t sci-fi tricks. They’re standard tools used by modern intelligence agencies and Tier-1 operators. Even the PowerShell-based spyware deployment described in THE FALLEN reflects real cyber-espionage playbooks.
No flashy movie montages.
No magical keyboards.
Just quiet, disciplined tradecraft.
Why it entertains: Readers feel like they’re getting a backstage pass into how covert operations actually work—clean, methodical, and unsettlingly plausible.
Welcome to the world behind the screen.
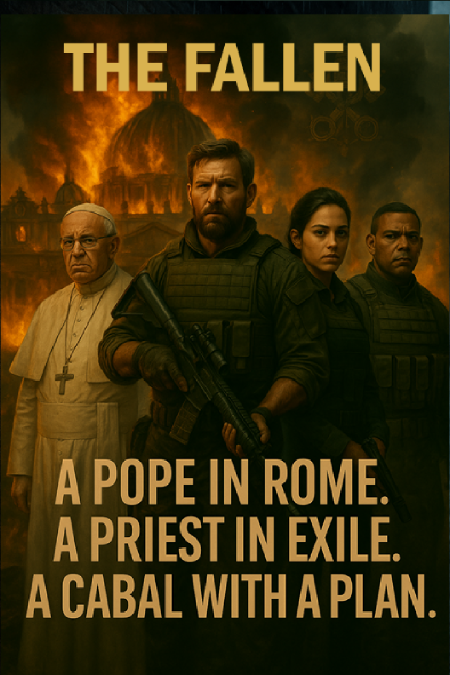
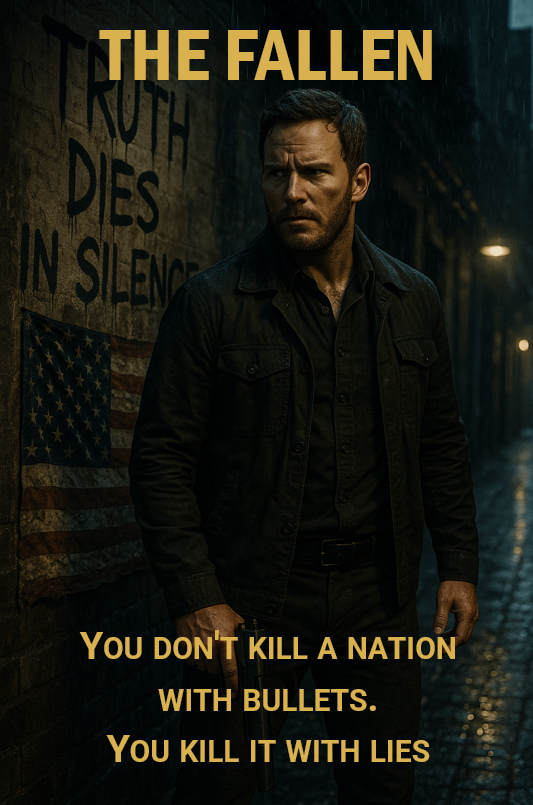
Welcome to THE FALLEN by Mark Slavik
BUY NOW – http://markslavik.com/
⚡ Faith. Power. Truth in the shadows.
#TheFallen #TheFallenNovel #MarkSlavik #PoliticalThriller #ThrillerReads #IntelligenceTradecraft #CyberOps #RealWorldEspionage #FaithAndPower #GideonsSword